Networking interview questions
Table of Contents
How does DNS work?
The Domain Name System, or DNS, is what allows you to use human-friendly domain names instead of numeric IP addresses. When you type a website name into your browser, DNS is responsible for finding the IP address that the network can actually connect to.
The first place a DNS request goes is the local DNS server, often called a recursive resolver. This server acts as an assistant for your computer. It takes your request and handles all the work needed to find the correct IP address.
Your computer usually learns the address of its local DNS server when it connects to a network. This information is provided automatically through DHCP by your router or network gateway. Along with an IP address and default route, your device is told which DNS server to use for name lookups. In some cases, this can also be configured manually in the network settings.
The local DNS server keeps a cache of recently resolved domain names. If the requested name is already in cache and still valid, the server can return the IP address immediately. This makes most DNS lookups very fast.
If the domain name is not found in cache, the local DNS server must ask other DNS servers for help. It starts at the top of the DNS hierarchy by contacting a root DNS server. Root servers do not know the final IP address, but they know which servers manage each top-level domain.
The root server responds with the address of a Top-Level Domain server, such as those responsible for.com,.org, or country-specific domains. The local DNS server then contacts the TLD server, which points it to the authoritative server for the requested domain.
The authoritative DNS server holds the actual mapping between the domain name and its IP address. Once this server responds, the local DNS server returns the IP address to your computer and stores it in cache for future use.
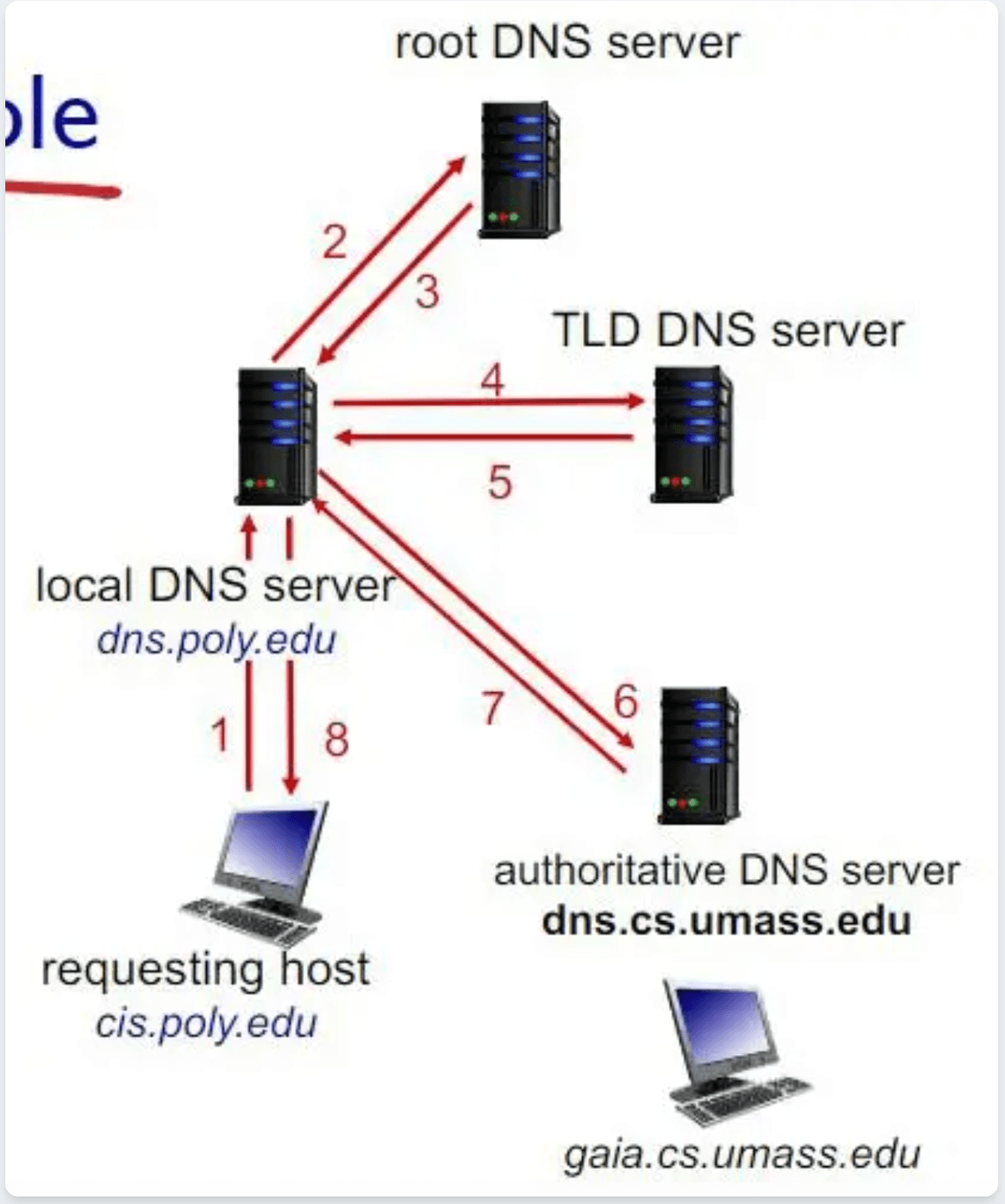
Iterative DNS query
In an iterative DNS query, each DNS server gives the best answer it has and tells the resolver where to go next. No server completes the lookup on its own. Instead, the local DNS server follows the referrals step by step until it reaches the authoritative server.
This means the local DNS server does most of the work, contacting the root server, then the TLD server, and finally the authoritative server before returning the result to the client.
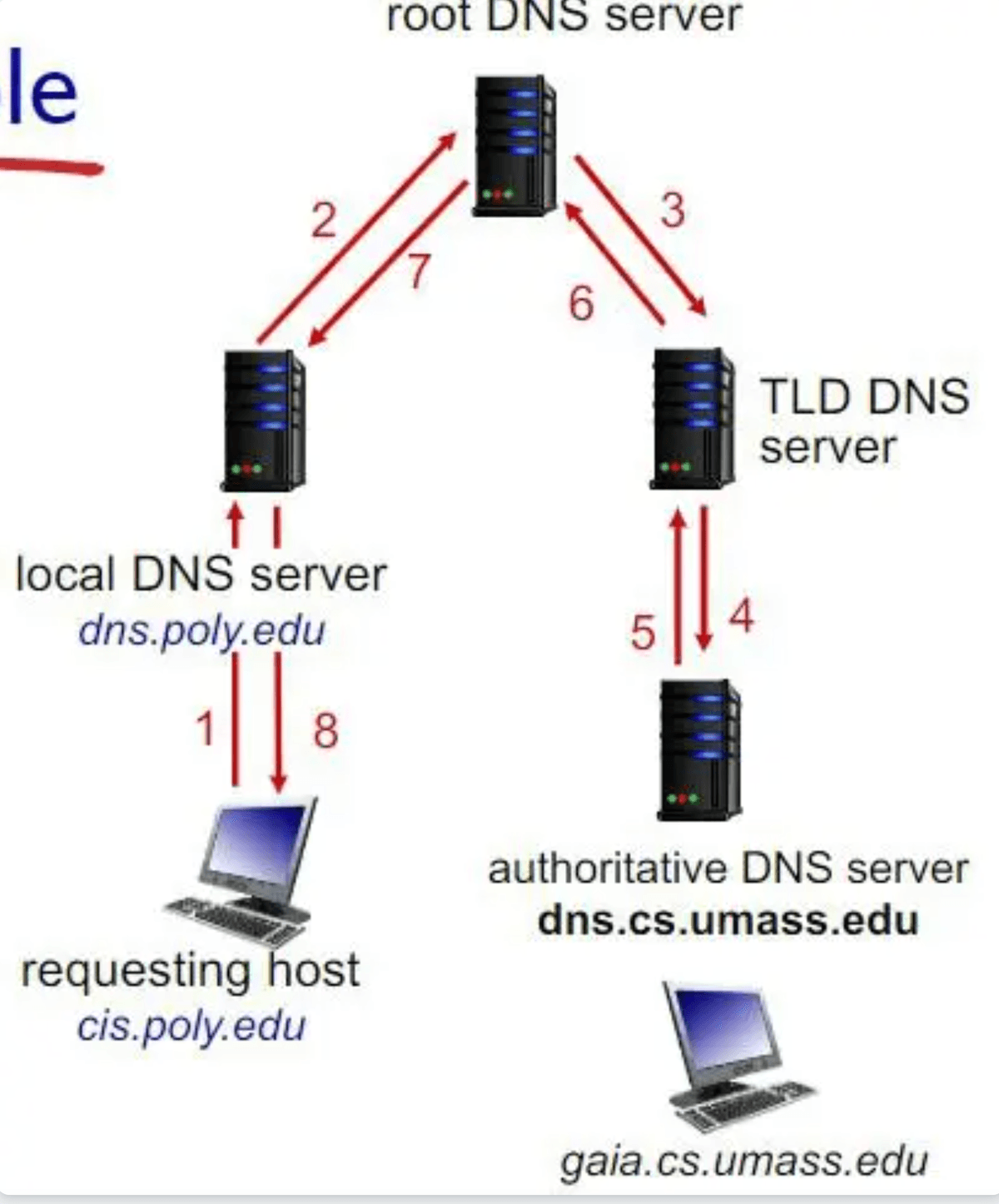
Recursive DNS query
A recursive DNS query is what your computer sends to the local DNS server. When making this request, your computer expects a final answer and does not want to contact any other DNS servers itself.
The local DNS server handles the entire resolution process on behalf of the client. Once it finds the IP address, it sends the result back and saves it in cache so future requests can be answered more quickly.
Cookies
HTTP itself is a stateless protocol, meaning each request is independent and carries no memory of previous interactions.Cookies are a mechanism used to introduce state into HTTP communication.
A cookie works through two main components. First, the Set-Cookie header is sent by the server in an HTTP response. The browser stores this cookie locally in a cookie file. Second, on subsequent requests to the same domain, the browser automatically includes the Cookie header in the HTTP request, allowing the server to identify the client.
When a user first visits a website, the server typically generates a unique session ID and stores it in a backend database. This ID is sent to the browser as a cookie. On future requests, the browser returns the session ID, enabling the server to retrieve the corresponding user data from its database.
In this way, cookies allow applications to implement features such as login sessions, shopping carts, user preferences, and analytics tracking, even though HTTP itself does not maintain state between requests.
TCP
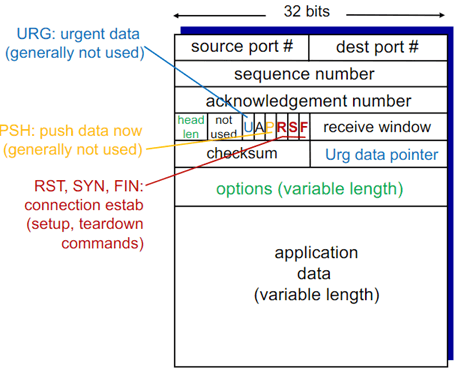
TCP provides reliable, in-order, full-duplex byte-stream communication between a client and a server. It ensures that bytes arrive exactly as sent, without loss, duplication, or reordering.
TCP guarantees reliability usingsequence numbers, acknowledgments(ACKs), timers, and retransmissions. Each byte is assigned a sequence number. The receiver acknowledges the next expected byte using the ACK number field. If the sender does not receive an acknowledgment within a reasonable time (close to theRTT(Round-Trip Time)), it retransmits the segment.
TCP does not provide guarantees for timing, minimum throughput, or security. It ensures correctness and reliability, but not performance guarantees.
Connection Establishment (Three-Way Handshake)
TCP connections are established using a three-way handshake. The client sends a segment with the SYN bit set. The server responds with SYN + ACK. Finally, the client replies with an ACK. This segment may contain client-to-server data. After this exchange, both sides can send data.
The server listens on a specific port number. When a client connects, the server creates a new socket dedicated to that client, allowing it to handle multiple concurrent connections. The combination of source IP and source port uniquely identifies each client.
Flow Control vs Congestion Control
Flow control ensures that a sender does not overwhelm the receiver's buffer. The receiver advertises available buffer space using the rwnd (receive window) field in the TCP header. The sender limits unacknowledged data to this value.
Congestion control protects the network itself from overload. When packet loss or delay suggests congestion, TCP reduces its sending rate. Flow control is end-to-end, while congestion control ensures network-wide stability.
Flow Control Protocols
Go-Back-N (GBN) and Selective Repeat (SR) are sliding window protocols used to achieve reliable and pipelined data transfer at the transport layer. Pipelining allows multiple packets to be sent before receiving acknowledgments, which improves throughput.
Go-Back-N (GBN)
In Go-Back-N, the sender can transmit multiple packets within a fixed window without waiting for individual acknowledgments. The receiver only accepts packets in order and uses cumulative acknowledgments.
For example, if packet 2 is lost but packets 3 and 4 are sent, the receiver discards packets 3 and 4 because packet 2 has not yet been received. The receiver repeatedly sends the last cumulative ACK (e.g., ACK1), indicating that it is still expecting packet 2.
When the sender’s timer expires, it retransmits all packets in the window starting from the lost packet. This guarantees reliability and ensures that all packets before the window have already been successfully delivered. However, it can be inefficient because correctly received packets are retransmitted unnecessarily.
Key characteristics of Go-Back-N: it uses cumulative acknowledgments, the receiver discards out-of-order packets, a single timer is maintained for the oldest unacknowledged packet, and all packets after a loss within the window are retransmitted.
Selective Repeat (SR)
In Selective Repeat, the receiver accepts and buffers out-of-order packets. Each correctly received packet is individually acknowledged.
For example, if packet 2 is missing but packet 4 arrives, the receiver buffers packet 4 and sends ACK4. Unlike Go-Back-N, the sender cannot assume that all packets before packet 4 have been received because acknowledgments are no longer cumulative.
The sender maintains a separate timer for each unacknowledged packet. When a timer expires, only the specific lost packet is retransmitted. This makes Selective Repeat more efficient than Go-Back-N, since correctly received packets are not resent.
TCP uses pipelining and cumulative acknowledgments similar to Go-Back-N, but it also includes additional mechanisms such as fast retransmit and selective acknowledgments (SACK), making it more advanced than pure Go-Back-N or Selective Repeat.
Reliable Data Transfer and Retransmissions
If packets or acknowledgments are lost, TCP uses timeouts and retransmissions. Duplicate segments are detected using sequence numbers, and the receiver discards duplicates. TCP uses cumulative acknowledgments, meaning an ACK confirms receipt of all bytes up to a certain sequence number.
Retransmissions are triggered by either a timeout or duplicate ACKs. In TCP Fast Retransmit, if the sender receives multiple duplicate ACKs (commonly three duplicates), it retransmits the missing segment immediately without waiting for the timeout.
Pipelining
TCP is a pipelined protocol, meaning it can send multiple segments without waiting for each one to be acknowledged individually. This improves throughput and network utilization.
Connection Termination
When a client wants to close the connection, it sends a TCP segment with the FIN bit set. After sending this FIN, the client can no longer send data, but it can still receive data from the server.
Upon receiving the FIN, the server responds with an ACK to acknowledge the client's request to close its sending side. At this point, the connection is considered half-closed. The server may continue sending any remaining data to the client.
When the server is ready to close its side of the connection, it sends its own FIN segment. The client then replies with an ACK to acknowledge the server's FIN. The connection is fully terminated only after both sides have sent and acknowledged a FIN.
In some cases, both sides may send FIN segments simultaneously. TCP handles this scenario correctly by acknowledging each FIN independently.
After sending the final ACK, the client enters the TIME-WAIT state and waits for twice the Maximum Segment Lifetime (2 × MSL) before fully closing the connection. This ensures that delayed or duplicate segments in the network do not interfere with future connections.
UDP
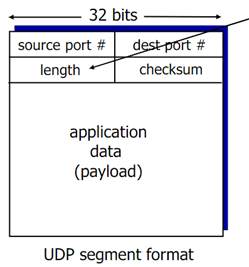
UDP (User Datagram Protocol) provides connectionless, best-effort delivery of data in the form of discrete units called datagrams. It is considered unreliable because transmitted data may be lost, corrupted, duplicated, or received out of order. It does not provide reliability, flow control, congestion control, timing guarantees, throughput guarantees, security, or connection setup. There is no retransmission mechanism. If a packet is lost, UDP does not attempt to recover it.
Since UDP is connectionless, no handshake is required before data is sent. A client can send data immediately, meaning communication can occur in a single round-trip time (RTT). In contrast, TCP requires at least one RTT to establish a connection before data transfer begins.
The sender explicitly attaches the destination IP address and port number to each UDP segment. The receiver extracts the sender’s IP address and port number directly from the received packet. A server typically uses a single socket to serve multiple clients, since there is no concept of a dedicated connection per client.
Unlike TCP, which treats data as a continuous byte stream and writes into a connection send buffer, UDP preserves message boundaries. The application has full control over what data is placed into each individual datagram.
The UDP length field specifies the total length of the UDP segment in bytes, including both the header and the application data. The application data itself is not stored in the UDP header but follows immediately after it. UDP includes a checksum field used to detect bit errors in the segment. While the checksum can detect that corruption has occurred, it cannot identify which specific bits were altered.
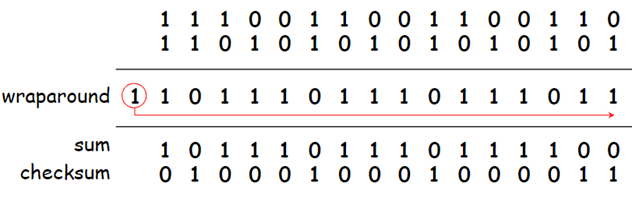
The checksum is computed by treating the UDP segment as a sequence of 16-bit integers. All 16-bit words are added together using binary addition, with the checksum field initially set to zero. If a carry is produced from the most significant bit, it is wrapped around and added back to the sum.
Finally, the one's complement of the computed sum is taken to produce the checksum value. At the receiver side, all 16-bit words including the checksum are summed together. If the result is all 1s, the segment is considered likely to be error-free, making validation both fast and efficient.
IP Layer
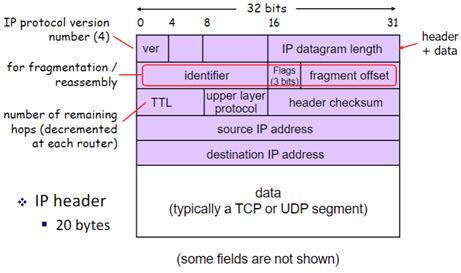
The Internet Protocol (IP) is responsible for delivering packets from a source host to a destination host across interconnected networks. The first field in the IPv4 header is the version number, which indicates the IP version being used. The Total Length field specifies the entire size of the datagram in bytes, including both the header and the data.
The Header Checksum field is used to detect errors in the IP header only. It does not verify the payload data (such as TCP or UDP segments). Each router that forwards the packet recomputes this checksum because certain header fields, such as TTL, may change during transmission.
The Protocol field indicates which upper-layer protocol is carried in the data portion of the packet, such as TCP or UDP. This allows the receiving host to deliver the payload to the correct transport-layer protocol.
The Time To Live (TTL) field prevents packets from circulating indefinitely in the network. Each time a packet passes through a router, the router decrements the TTL value by one. If the TTL reaches zero, the packet is discarded.
Different network links may have different Maximum Transmission Units (MTU), which define the largest amount of data that can be carried in a single link-layer frame. If an IP datagram exceeds the MTU of a link, it may be fragmented into smaller pieces by a router. During fragmentation, one large IP datagram is split into multiple smaller datagrams. Each fragment contains a copy of the original IP header, with modified fields such as total length and fragmentation information. Reassembly of fragments occurs only at the final destination host, not at intermediate routers.